Introduction
Sextortion – threatening to expose sexual images of someone if they don’t yield to demands- has been a source of harm to youth for some time. In the last several years, concerns about a unique type of sextortion – financial sextortion – have been on the rise. Reports of financial sextortion revolve around demands for money and predominantly target boys, and young men. In addition, financial sextortion marks the emergence of new organized offenders leveraging technology to target and extort minors at scale.
In partnership with the National Center for Missing & Exploited Children (NCMEC), this research examines more than 15 million reports made to the CyberTipline from 2020 to 2023 to pinpoint cases of sextortion and examine the evolving scale and nature of financially motivated sextortion. Importantly, while sextortion can affect all ages, this report focuses explicitly on the sextortion of minors.
This page reviews several key findings from Thorn’s report on trends in financial sextortion and identifies opportunities for action to safeguard young people from this growing threat effectively. To read the complete research report and explore its findings in greater detail, please download the PDF.

 NCMEC received an average of 812 sextortion reports per week.
NCMEC received an average of 812 sextortion reports per week. More than two-thirds of these reports appear to be financially motivated.
More than two-thirds of these reports appear to be financially motivated. 90% of victims detected in NCMEC reports were male, aged 14 to 17.
90% of victims detected in NCMEC reports were male, aged 14 to 17. Among reports that include details on victim impact, 1 in 6 discuss thoughts of suicide or self-harm.
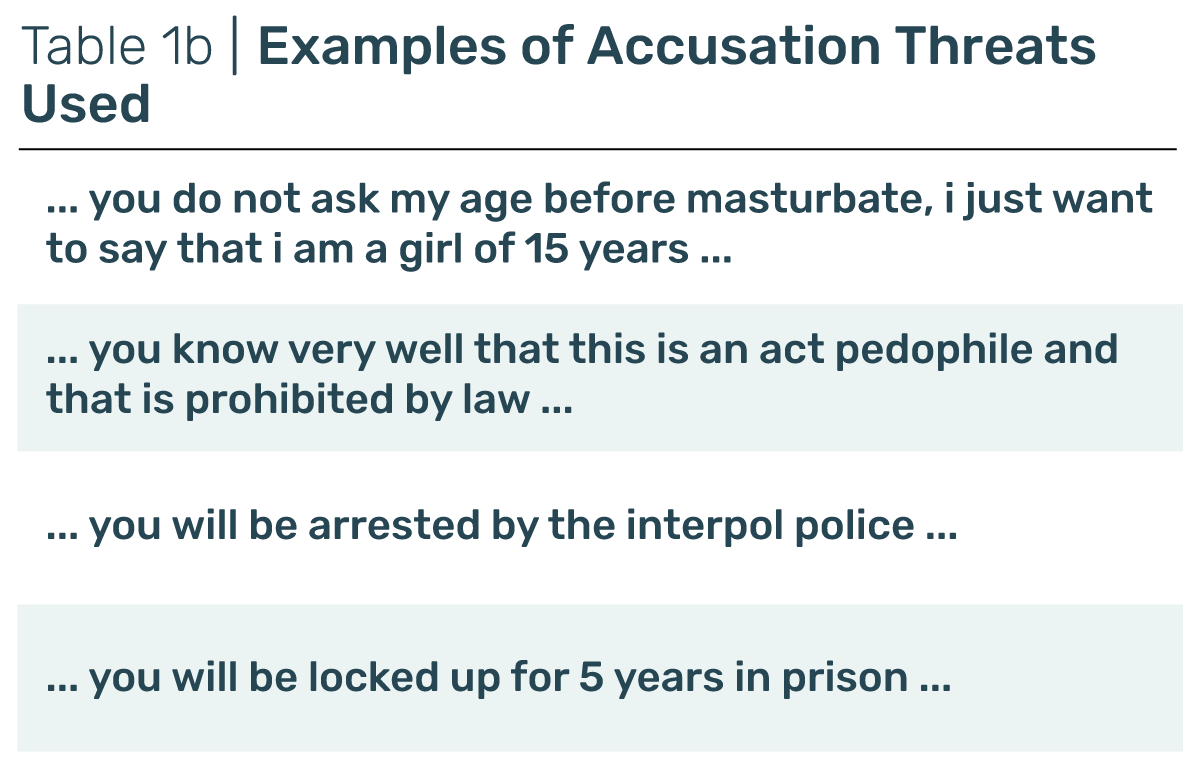
Among reports that include details on victim impact, 1 in 6 discuss thoughts of suicide or self-harm. 38% of reports with chat logs included exaggerated impacts and/or threats of ruining the victim’s life.
38% of reports with chat logs included exaggerated impacts and/or threats of ruining the victim’s life.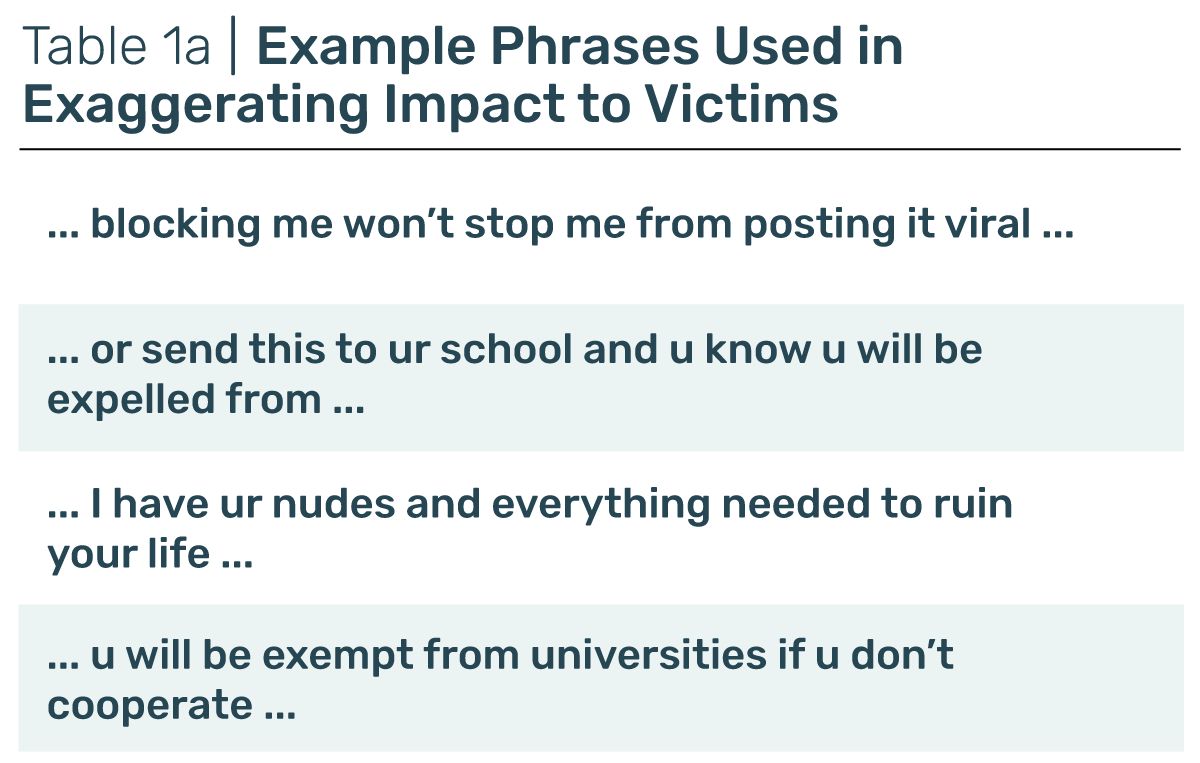
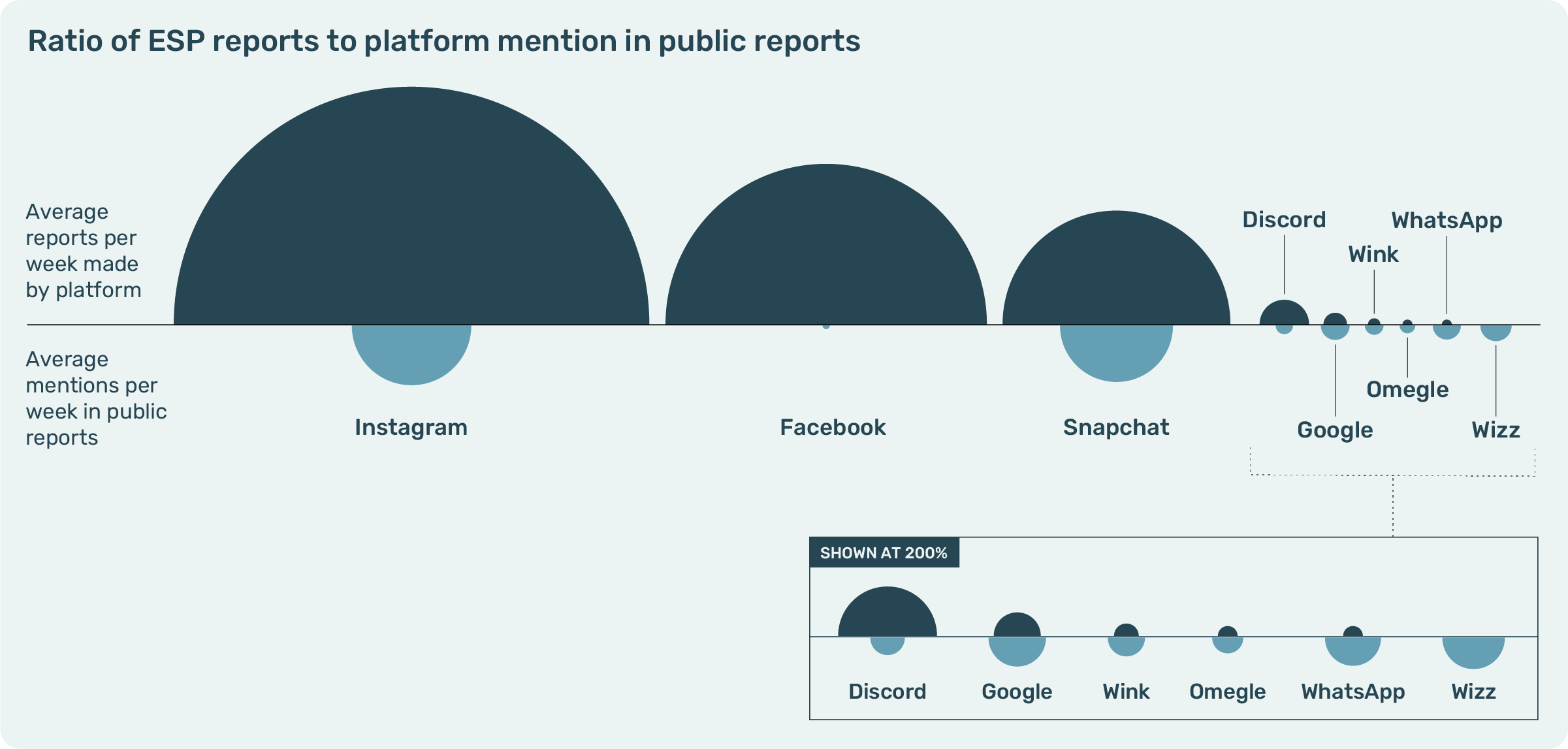
 1 in 10 reports with information about the platform of first meeting mentioned Omegle or Wizz as an initial contact point.
1 in 10 reports with information about the platform of first meeting mentioned Omegle or Wizz as an initial contact point.